Multi-factor authentication is now everywhere and for good reason. As cyber threats like phishing attacks and password breaches continue to rise, multi-factor authentication has been the go-to solution for securing accounts and systems across the board.
But the challenge isn’t just adopting MFA in Microsoft 365, it’s maintaining it! With so many authentication methods available, enforcing a consistent and secure policy across an entire organization is easier said than done.
Microsoft addressed this with System-Preferred MFA. Instead of leaving the decision to users or admins, Microsoft automatically enforces the most secure authentication method available for each user.
Announced in early 2023, it has since become a reliable option for organizations ready to strengthen their authentication policies. In this blog, we’ll cover how it works, how to enable it, and what it means for your organization.
What is System-preferred Multi-factor Authentication?
For IT administrators managing authentication across a large user base, keeping everyone on the most secure sign-in method is a constant challenge. System-Preferred MFA addresses this directly.
With the system-preferred MFA enabled, Microsoft evaluates all the authentication methods a user has registered and automatically prompts them to sign in using the most secure one, regardless of what they’ve set as their default.
Let’s see an example for this case – Consider a user registered for both phone call authentication and the Microsoft Authenticator push notification method, with phone call set as their default. Normally, they’d be prompted to authenticate via phone call. With System-Preferred MFA enabled, Microsoft overrides that and prompts the Authenticator push notification instead, since it’s the stronger option out of the two. (I have covered how does Microsoft determine the most secure method below)
Note: The system-preferred MFA isn’t limited to users specified by authentication method policies; it also extends to users who have enabled MFA through the legacy MFA policy (per-user MFA).
Different Ways to Manage System-preferred MFA in Microsoft 365
Now that we’ve seen how this feature can help save us from potential threats, let’s move on to the steps to enable this important security feature. There are two ways to enable system-preferred MFA in Microsoft 365, and they are:
- Enable system-preferred MFA in the Entra admin center.
- Manage system-preferred MFA through Graph API.
But before we delve into the steps, it’s essential to note that there is a restriction that comes with it, which is –
➤ You can only include/exclude one group at a time. (The groups can be either dynamic or nested groups.)
Enable System-preferred MFA in the Entra Admin Center
System-Preferred MFA is enabled by default in Microsoft 365, so you’re likely already using it. Here’s how to check. 👇
- Sign in to the Microsoft Entra Admin Center as at least an Authentication Policy Administrator.
- Navigate to Entra ID → Authentication Methods → Settings → System-Preferred MFA.
- Unless configured otherwise, system-preferred authentication stays enabled and Microsoft-managed across all users.
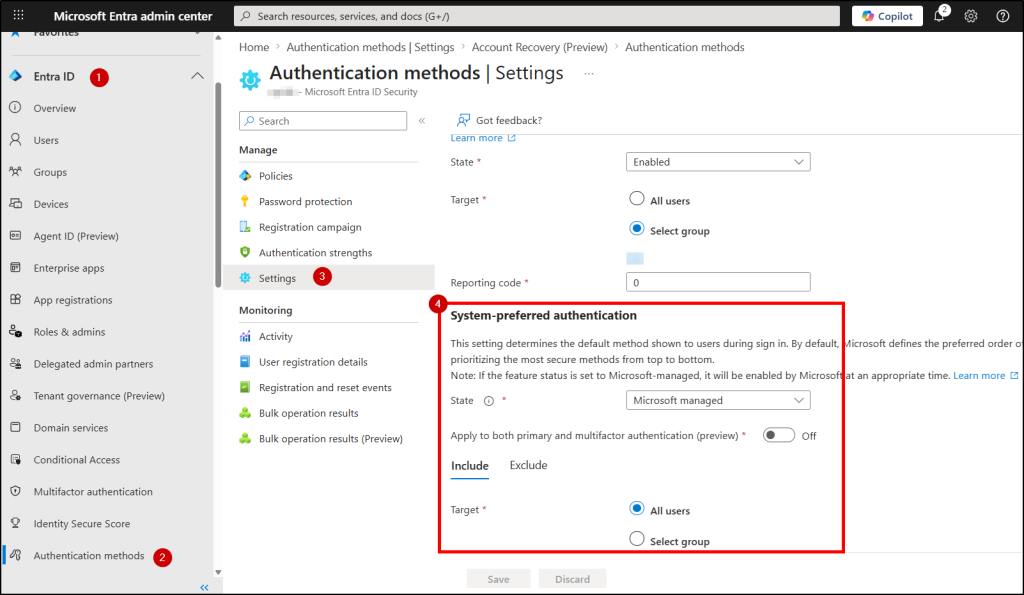
4. You can customize further and scope it to specific users or groups under the ‘Target’ section. Keep in mind that excluded groups always take precedence over included ones.
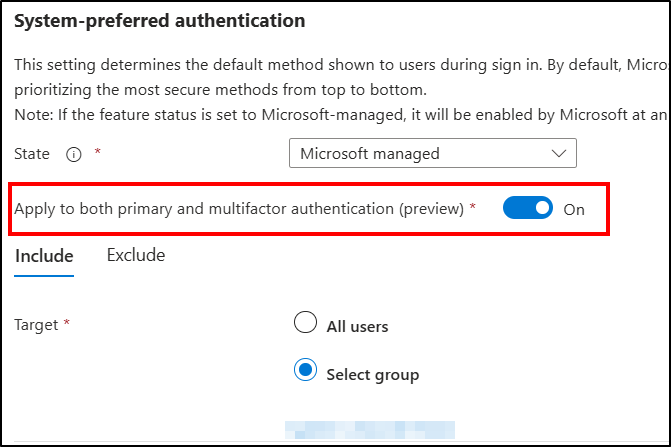
| Extra toggle (important): There’s a new option that’s in preview: Apply to both primary and multifactor authentication (preview) If you turn ON → extends device-preferred credential logic to both primary and secondary authentication. If left turned OFF → applies to the second factor only(default behaviour). |
5. Click Save, and you’re done.
How to Manage System-preferred Authentication through Graph API
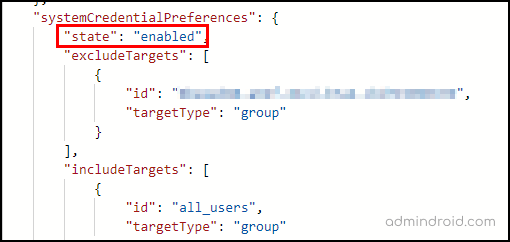
Log in to the Microsoft Graph developer portal and ensure that you have the permission Policy.ReadWrite.AuthenticationMethod granted.
You can use the following sample code to enable system-preferred MFA for all users and exclude a specific group.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 |
PATCH https://graph.microsoft.com/beta/policies/authenticationMethodsPolicy Content-Type: application/json { "systemCredentialPreferences": { "state": "enabled", "excludeTargets": [ { "id": "d1411007-6fcf-4b4c-8d70-1da1857ed33c", "targetType": "group" } ], "includeTargets": [ { "id": "all_users", "targetType": "group" } ] } } |
The above query disables system-preferred MFA for the selected group and overrides other users’ weaker authentication with their strong MFA authentication method. Now, if you want to check whether the code works as expected, you can use the following query and check:
|
1 |
GET https://graph.microsoft.com/beta/authenticationMethodsPolicy |
How Microsoft Decides the Best MFA Option for Users
System-preferred MFA isn’t just a fixed list; it works more like a smart selector. During sign-in, Microsoft looks at what methods the user has registered, checks what’s actually supported on the device, and then prompts the most secure option available in that context.
The ranking itself isn’t permanent. Microsoft keeps updating it as new threats emerge and stronger authentication methods become available, so what’s “best” today can evolve over time.
At a high level, methods are grouped by how well they hold up against modern attacks:. To keep things simple, methods are broadly prioritized like this:
- Phishing-resistant → hardest to compromise
- Passwordless → remove password risk entirely
- Traditional MFA → adds a second layer, but is still phishable
- Legacy methods → weakest, mostly fallback options
With that context, here’s how the current ranking breaks down:
| Method | Reason for Ranking |
|---|---|
| Rank 1: Temporary Access Pass (TAP) Satisifies: 1FA + MFA | TAP is at the top not because it’s “strongest” in general use, but because it’s controlled, short-lived, and issued by admins. → It’s designed to safely bootstrap access. |
| Rank 2: Passkey (Covers security keys, passkeys in the Authenticator app, synced passkeys, Windows Hello for Business, and macOS Platform SSO.) Satisifies: 1FA + MFA | These are the gold standard right now. They don’t rely on shared secrets and can’t be replayed or intercepted either. → This is why passkeys and certificates rank so high. |
| Rank 3: Certificate-Based Authentication (CBA) Satisifies: 1FA + MFA | Same phishing-resistant strengths as passkeys, with flexible auth satisfaction. |
| Rank 4: Microsoft Authenticator (Push Notification) Satisifies: 1FA + MFA | Strong and convenient, but still vulnerable to MFA fatigue and push spamming. |
| Rank 5: External MFA Satisifies: MFA | Depends on the third-party provider’s security posture. |
| Rank 6: TOTP (Hardware/Software) Satisifies: MFA | Better than passwords alone, but codes can be phished, and users can be tricked into sharing them. |
| Rank 7: Telephony (SMS/Voice) Satisifies: MFA | SIM swap attacks and interception risks make this increasingly discouraged. |
| Rank 8: QR Code Authentication Satisifies: 1FA | Exists for frontline/edge scenarios, not a security-first choice |
| Rank 8: Password Satisifies: 1FA | Weakest, always a fallback, never a preference. |
A couple of realities to keep in mind:
- Users still have a choice. They can always cancel and pick a different registered method during sign-in.
- Conditional Access takes priority. Any CA policies requiring specific methods will always override this ranking.
- Device-preferred credential changes the equation! When enabled, the system checks what’s actually available on the user’s current device before picking a method. This helps to avoid situations like prompting for a passkey on a device that doesn’t support one.
End User Experience: What Users See During Secure Sign-in
To see how this works in practice, let’s walk through a real example with the user: authy@contoso.com.
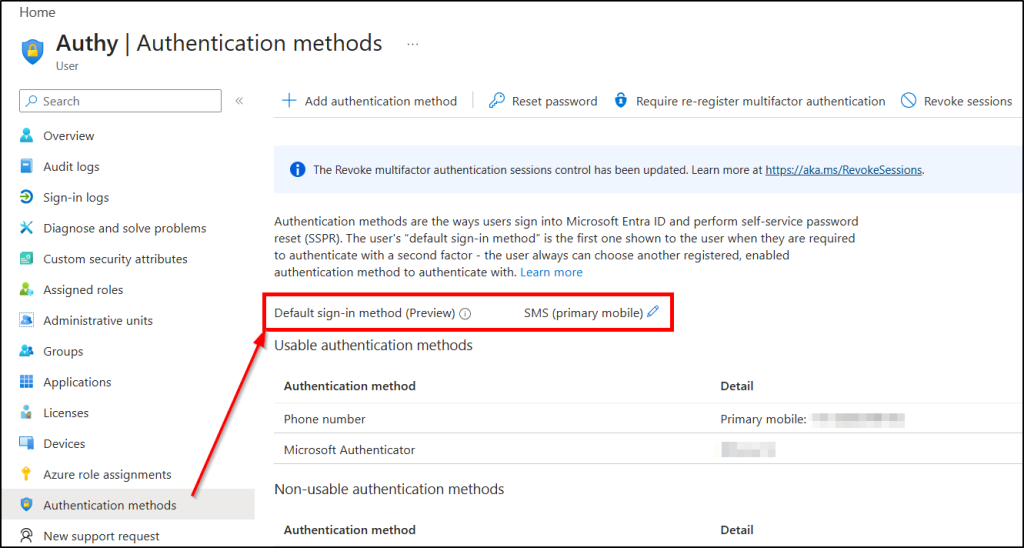
Before testing, you can check the user’s default authentication method in the Entra admin center. In this case, SMS is set as the default, with a few other MFA methods also registered.
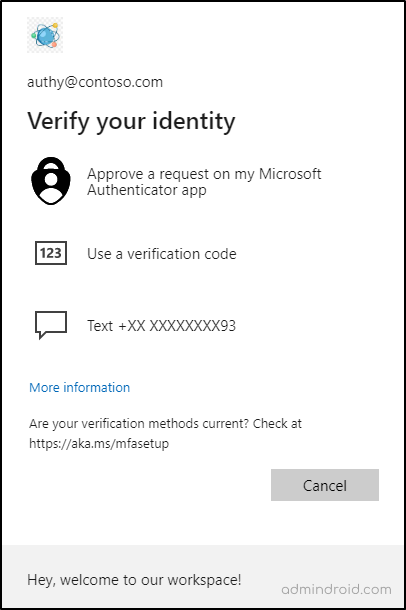
Without system-preferred MFA, Microsoft prompts the user with their default method (SMS in this case), while still allowing them to choose from other available options.
Once System-Preferred MFA is enabled, Microsoft evaluates all registered methods and steps in with the strongest one. Here, among the available methods, Microsoft Authenticator push notification is considered stronger than SMS. So instead of asking the user to choose, the system directly prompts them with that method.
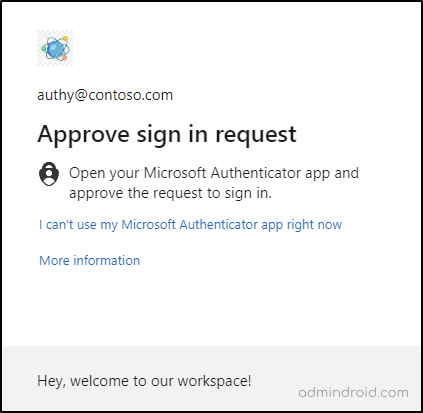
This is definitely a more robust and reliable feature, isn’t it? The difference is clear, the user is automatically guided toward a stronger authentication method without any manual reconfiguration.
That’s it! I hope we have shown a clear idea of how this system-preferred MFA will work for your organization. System-preferred MFA quietly improves both security and usability. It reduces reliance on weaker methods like SMS while nudging users toward safer options.