As cyber threats become increasingly sophisticated, protecting your organization’s sensitive accounts such as priority accounts and glass break accounts is paramount. Are you looking to secure your C-suite executive accounts in your organization or concerned about implementing compliance control over certain security groups that handle sensitive applications? The new solution is adding those accounts or security groups into the restricted management administrative units in Microsoft Entra ID. It helps protect important accounts from unauthorized modification and allows only a specific set of administrators to access them. This feature is currently in preview.
Before jumping into the topic, let’s first understand what an administrative unit Entra ID actually is!
Delegate Administrative Tasks Using Administrative Units in Microsoft Entra
According to Microsoft, “an administrative unit is th Entra ID resource that acts as a container for other Entra iD resources”. They are like compartments within an organization that gives certain people special powers to manage and control specific areas, such as departments or regions. It’s one of the ways to limit and define who has administrative permissions and where those permissions apply.
How Do Administrative Units Work in Entra ID?
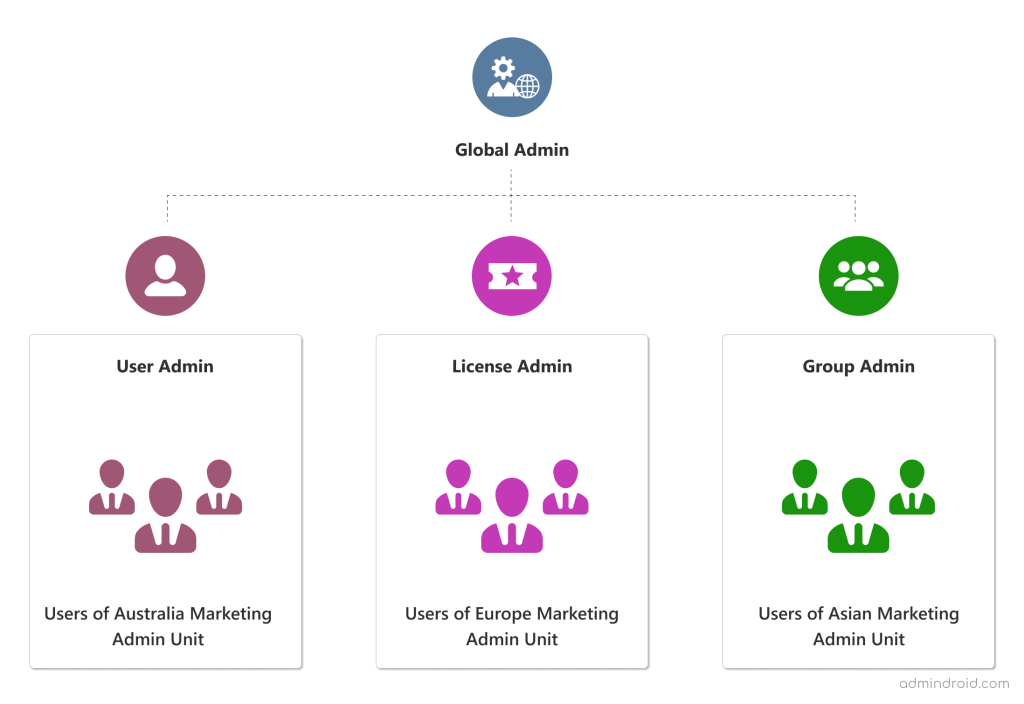
Let’s consider the scenario of a company that has multiple departments across different regions. Say, Marketing department, which has teams located in various countries. Instead of assigning a User Administrator and giving them rights to manage all the users in the organization, here’s how admin units can be used in this scenario:
- The Global Administrator or a Privileged Role Administrator in Azure AD creates separate admin units for each region where the Marketing department operates. For example, admin units can be created for Australia, Europe, and Asia.
- Within each admin unit, the Global Administrator assigns a user as the administrator for that specific region.
- The Global Administrator then adds the respective Marketing team members from each region to their corresponding admin units. For instance, all the European-based marketing team members are added to the Europe Marketing admin unit.
- Now, the assigned administrators can manage the Marketing team members within their respective admin units.
How to Create Administrative Units in Entra ID?
You can create an administrative unit by using either the Entra ID portal, PowerShell, or Microsoft Graph.
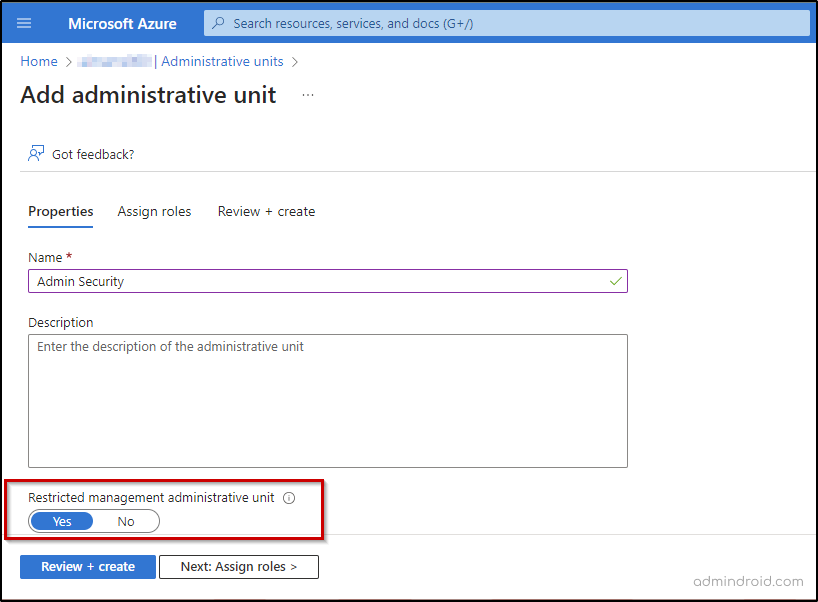
To create a new administrative unit in the Entra ID portal, follow the steps given below.
Step 1: Sign into the Microsoft Entra admin center.
Step 2: Select Identity -> Roles & admins -> Admin units.
Step 3: Add a new administrative unit by naming it.
Step 4: Enter the description of the administrative unit and set the ‘Restricted management administrative unit’ toggle to ‘Yes’.
Step 5: Assign roles from the ‘Assign roles’ tab based on the role description.
Step 6: Include users to the role scope and then click ‘Add’.
Step 7: After reviewing the administrative unit, select Create.
After creating the new administrative unit in Entra ID, you can then proceed with adding objects to the administrative unit by selecting respective units.
Here is where the importance of restricted management administrative units comes in! When you don’t want a User Administrator of an admin unit to manage accounts of a Global Administrator, you can add the Global Administrator account into a restricted management administrative unit and prevent unauthorized access.
It ensures that only users who have been assigned a role within the scope of that unit can manage the Global Administrator account.
Restricted Management Administrative Units in Entra ID
Restricted management administrative units add an extra layer of security to important accounts in the organization. When an account is added to one of these units, only users with assigned roles in that unit can manage it.
Difference Between Administrative Units and Restricted Management Administrative Units:
Administrative Units in Entra ID
- Administrative unit limits their administrative permissions to only the resources in that unit.
- However, Global Administrators still have the ability to manage all resources, including those in administrative units, even without specific roles assigned at the unit level.
Restricted Management Administrative Units in Entra ID
- When an account is added to such a restrictive management administrative unit, only users with assigned roles at the unit level can manage it. This applies to Global Administrators as well.
- If a Global Administrator does not have a role assigned at the unit level, they cannot manage the accounts within that unit.
License Requirements for Restricted Management Administrative Units
Restricted management administrative units require an Entra ID Premium P1 license for each administrative unit administrator, and Entra ID Free licenses for administrative unit members. However, creating administrative units can be done by having an Entra ID free license.
Who Can Create Restricted Management Administrative Units in Entra ID?
Global Administrators and Privileged Role Administrators can create a restricted management administrative unit in Entra ID.
What Objects Can Restricted Management Administrative Units Include?
All except mail enabled security groups and distribution groups can be members of restricted management administrative units. It is important to note that placing objects in restricted management administrative units severely restricts who can make changes to the objects.
What are Referred to as Objects in Entra ID?
Some of the Azure AD object types are users, devices, security groups, Microsoft 365 groups, mail- enabled security groups, and distribution groups.
FAQs on Restricted Management Administrative Units in Entra ID
1. Who can Modify Objects within a Restricted Management Admin Unit?
To make changes to the Azure Active Directory properties of objects within a restricted management admin unit, administrators must be,
- Explicitly assigned to the scope of a restricted management administrative unit.
- Assigned at the scope of another restricted management administrative unit, where the object is a member.
2. How to Grant Application Access to Modify Objects in Restricted Management Administrative Units?
By default, applications are unable to make modifications to objects within restricted management administrative units. To allow an application, the ability to manage objects within such units, you need to assign the “Directory.Write.Restricted” permission.
3. Can a User be Added to More Than One Administrative Unit?
A user or a group can be in multiple administrative units, but the admin units cannot be nested.
4. What Types of Operations are Blocked in Restricted Management Administrative Units?
| Operation Type | Blocked | Allowed |
| Read basic information about a user, such as their username and profile picture. | ✅ | |
| Change the properties or attributes of a user account, group, or device within Azure AD. | ❌ | |
| Remove a user account, group, or device from Azure AD. | ❌ | |
| Change or reset the password for a user account | ❌ | |
| Make changes to the list of owners or members of a group within a restricted management administrative unit. | ❌ | |
| Include users, groups, or devices from a restricted management administrative unit as members of groups in Azure Active Directory. | ✅ | |
| Modify email and mailbox settings for a user account within a restricted management administrative unit, typically in Microsoft Exchange. | ✅ | |
| Enforce specific policies or settings on a device within a restricted management administrative unit by utilizing Microsoft Intune. | ✅ | |
| Grant or revoke ownership privileges for a group on a SharePoint site, giving them administrative control over the site. | ✅ |
Limitations of Restricted Management Administrative Units
Below are some of the limits of restricted management administrative units in Entra ID.
- Once an administrative unit is created, the restricted management setting cannot be changed.
- Azure AD Privileged Identity Management cannot be used to manage groups in a restricted management administrative unit.
- In a restricted management administrative unit, membership modification is not allowed for role-assignable groups. Only Global Administrators and Privileged Role Administrators can modify membership.
- Certain actions may not be possible in a restricted management administrative unit if the required role cannot be assigned at the administrative unit level. For example, a Global Administrator in a restricted management unit cannot have their password reset by any other administrator.
- When deleting a restricted management administrative unit, it may take up to 30 minutes to remove all protections from the former members.
Lastly, it is crucial to exercise caution when creating a restricted admin unit because once permissions are granted, they cannot be undone.
Thanks for reading! I hope this blog will help you with everything that you need to know to create and manage restricted management administrative units in Azure AD. For further assistance, feel free to reach out in the comment section.






