On Day 12 of Cybersecurity awareness month, learn to use priority accounts as tags today. Stay tuned for more blogs in the Cybersecurity blog series.
CISCO’s 2021 Cybersecurity threat trends report suggests that at least one person clicked a phishing link in around 86% of organizations. The company’s data suggests that phishing accounts for around 90% of data breaches. Most of these attacks are thrown at executives and heads of the organization who handle critical information. So, it is necessary to pay extra attention to these accounts by providing good security. With the Priority Accounts capability, a Microsoft 365 admin can set specific users as priority accounts, so that they can utilize specially designed app features for additional security.
“It is not data that is being exploited, it’s people that are being exploited”.
– Edward Snowden
What are Priority Accounts in Microsoft 365?
Priority accounts are users in an organization who manage sensitive information such as financial data, product development information, etc. More precisely, these users are C-level or D-level executives other than regular employees. Applying Priority account tags to these users helps to target your most important data reports.
Priority Accounts Vs Regular Employee Accounts
In any organization, there are mainly two types of information. Information that is allowed only for those who hold the key to that organization, and the rest that is not confidential. Priority accounts work for users who hold the keys. Being a Priority account gives the user more heuristics and visibility in reports than a regular employee account.
At the outset, Microsoft introduced two capabilities that support priority accounts and has promised to add more features in the future. Those two capabilities are,
- Priority account protection
- Premium Mail Flow Monitoring
| Feature | Required License |
| Priority account protection | Microsoft Defender for Office 365 Plan 2, including those with Office 365 E3, Office 365 E5, Microsoft 365 E5, or Microsoft 365 E5 Security. |
| Premium Mail Flow Monitoring | A license count of at least 5,000, from either one or a combination of the following products: Office 365 E3, Microsoft 365 E3, Office 365 E5 Microsoft 365 E5. In addition to the license requirement, at least 50 monthly active users for one or more core workloads – Teams, OneDrive for Business, SharePoint Online, Exchange Online, and Office apps. |
Priority Account Protection
Priority Account Protection is turned on by default for pre-identified critical users. As security admins, you can also disable it by navigating to the Microsoft 365 Defender > Settings >Email and collaboration>Priority account protection. Priority account protection offers the following benefits.
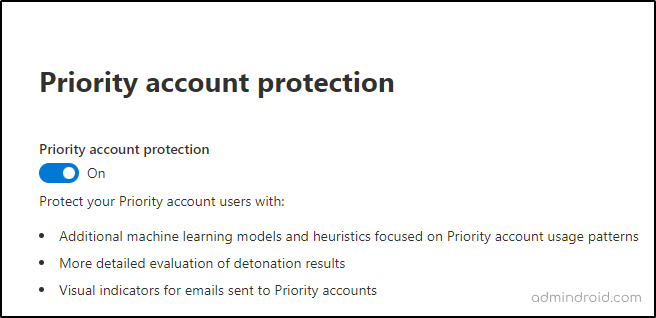
Additional heuristics: Microsoft’s analysis of mail flow indicates that priority account protection offers additional heuristics for executives other than a regular employee.
Additional visibility in filtering: The priority account tag filter provides additional visibility for alerts, reports, and investigations. The new email entity page shows Priority Account tag as an indicator on email messages.
Now, let’s check the benefits of Priority Accounts by configuring them as tags!
Priority Account Tagging
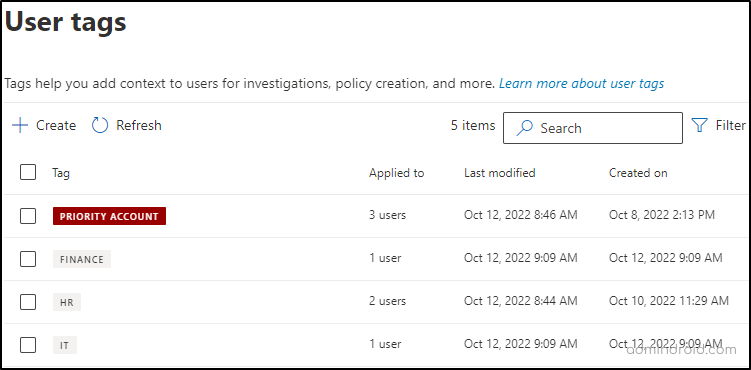
Priority account in Microsoft 365 Defender is supported as user tags. Tagging highlights priority accounts and helps you give special attention to them. These tags can be applied as filters in alerts and reports for easily identifying the threats posed on priority accounts. Admins can pick up users that are likely to be compromised by attackers and pose a tag on them.
Tagging your priority accounts adds highlighted visibility to email threats and helps to filter them across Microsoft 365 Defender portal. Adding users to priority tags is simple.
To apply tags to priority accounts, follow the steps given below.
- Scroll down to Settings in the navigation bar.
- Select Email and Collaboration > User Tags > Create.
Note: The Priority Account tag is already created for you by default.
- Add users to the priority tag by selecting edit.
- Then Add members -> Add.
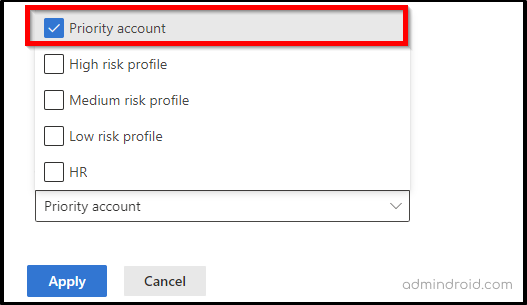
You can also create custom tags such as HR, IT, etc. by selecting +Create from User Tags.
Who Can Manage User Tags?
The table given below depicts the role groups a user must be a member of, to perform various operations.
| Operation | Role Groups |
| Create, modify and delete custom tags Add and remove members from existing custom user tags | Organization Management or Security Administrator |
| Add or remove members from the Priority Account tag | Security Administrator and Exchange Admin |
| Read-only access to user tags | Global Reader, Security Operator, or Security Reader role groups. |
Note: If you are a Global Administrator, you are already a member of the Organization Management role group.
How Does Tagging Priority Accounts Work?
After tagging users as priority accounts, you can see the settings becoming effective across Microsoft 365 Defender locations as listed below.
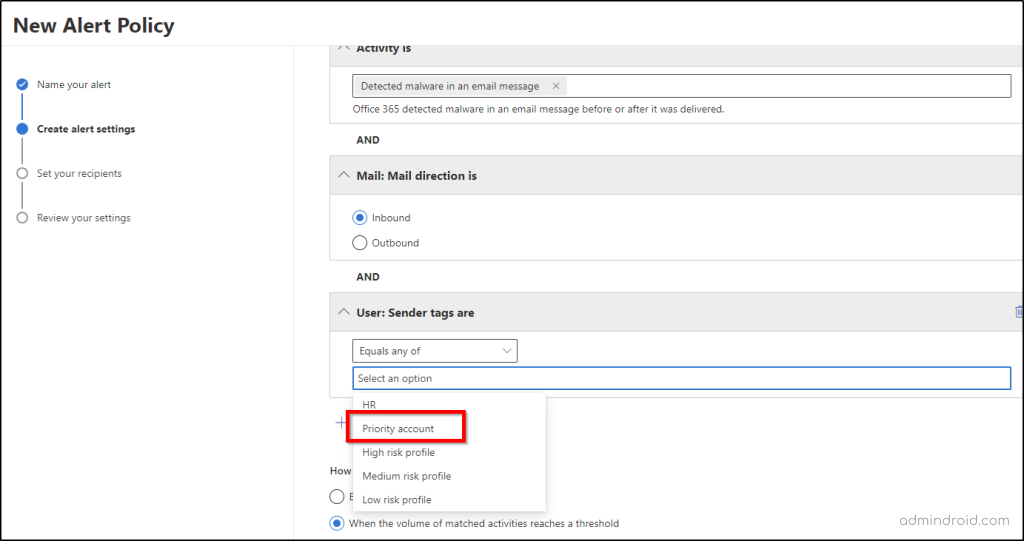
Alert Policies
You can create an alert policy that generates email notifications to admins anytime a priority account receives a malicious email.
You can do this by selecting Policies and rules from the navigation bar. After naming the alert policy, add the condition as sender tags, then select Priority account from the drop-down menu and > Select recipients for email notifications > Review your settings > Done.
Actions and Submissions
When a priority account reports a malicious email, you can easily filter them from this section. Under User reported messages, you will find those users tagged as priority accounts.
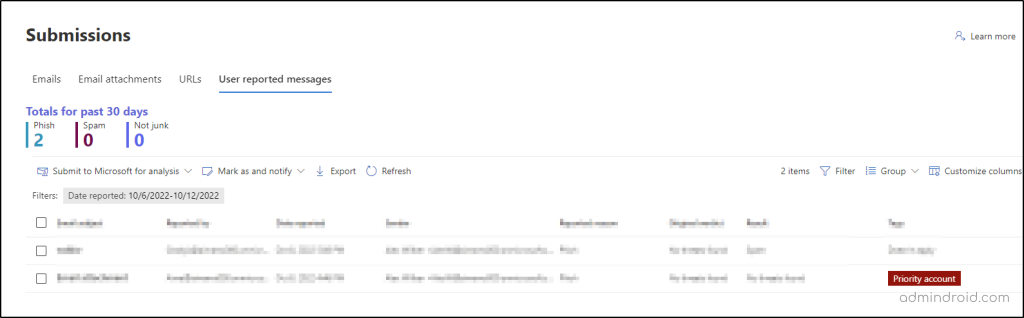
You can filter only priority accounts by selecting Tag as Priority account from the filter option.
Explorer
The explorer tab of the navigation bar is another use case for priority accounts. The tags column in the email grid displays the priority accounts first as a result of tagging.
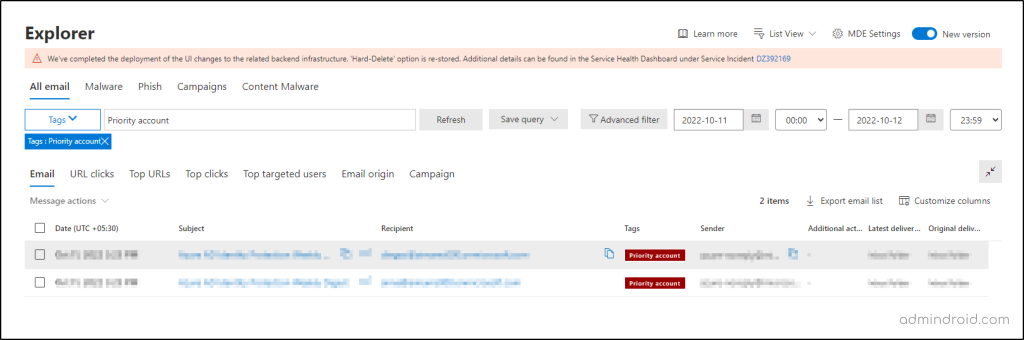
You can filter priority accounts by selecting Tags from the filter dropdown and entering priority account as the value in the entry box, then refresh.
Threat Protection Status
The Threat protection status report provides information about threats found prior to email delivery, covering relevant detection technologies, policy types, and delivery actions.
Reach this page by navigating to Reports > Email and collaboration > Threat Protection Status.
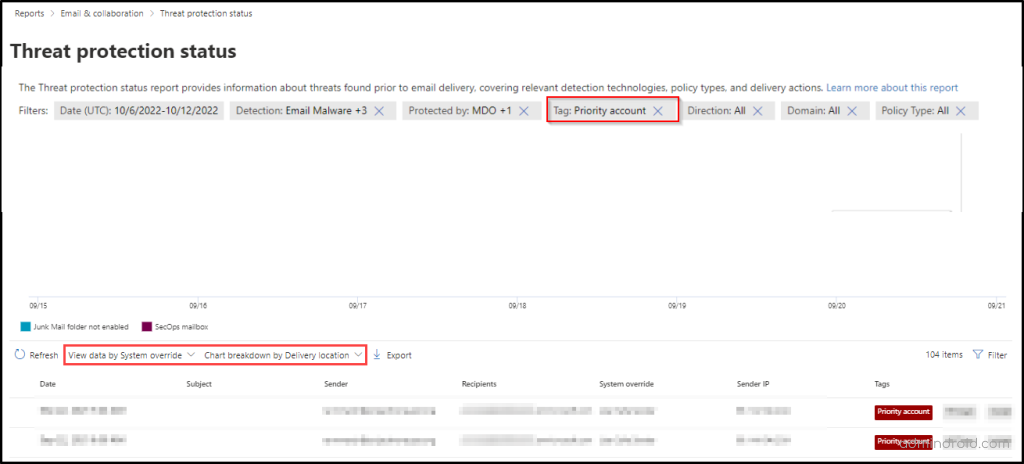
Now, you can filter the priority account tags by selecting Priority account filter from the drop-down.
Campaign Views
A campaign is a coordinated email attack against one or many organizations. Campaign Views is a feature in Microsoft Defender for Office 365 Plan 2 that identifies and categorizes phishing attacks. In Campaign Views, you can filter priority accounts to get a big picture of the attacks on them. You can get to Campaign Views from Email & collaboration > Campaigns.
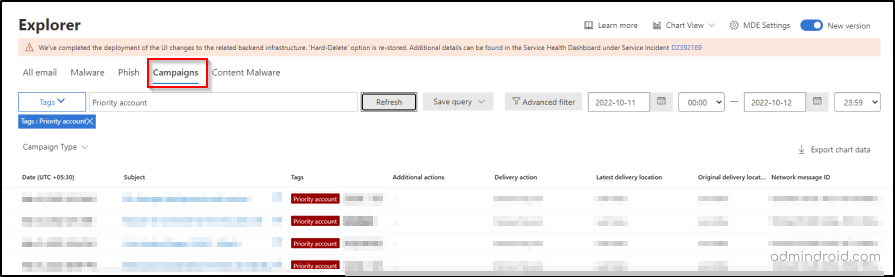
From the Campaign type dropdown, you can select the filter tag and enter the value as ‘Priority account’, and refresh the results to view the campaign attacks posed on priority accounts in your organization.
URL Threat Protection Report
URL protection reports provide insights into the number of URL clicks by users in the organization and the results of the click. It helps in identifying and addressing any potential security risks within the Office 365 enviroment. You can find this report by navigating to Emal & collaboration > URL protection report. Microsoft has also added the priority accounts tag filter into the URL protection report that makes it even easier to focus on the URL clicks by accounts that hold the key in the organization.
Points To Remember
- User tags can be applied to mailbox users only.
- The in-built priority account system tag cannot be removed.
- You can monitor up to 250 priority accounts.
Other Security Recommendations for Priority accounts
Microsoft recommends providing additional protection to these priority accounts by using the following features.
- Increase sign-in security for priority accounts by configuring multi-factor authentication.
- Disable legacy authentication globally for priority users.
- Configure Client Access Rules to disable POP3 and IMAP4.
- Use Strict Profile preset for implementing preset security policies for priority accounts.
- Train priority account users about the concepts of recognizing attacks.
Premium Mail Flow Monitoring for Larger Tenants
As stated above in the license requirement table, organizations that satisfy the requirements for configuring Premium mail flow monitoring can use this feature effectively for monitoring mail flow and apply threshold for failed or delayed mails by configuring them in the Exchange Admin Center. As my test account doesn’t fall into the required eligibility, I could not test it out for you. If you do, please check it out and let me know in the comments.
I hope the blog manages to help you understand the concepts of priority accounts and their usage. Feel free to reach us in the comments for any assistance.
Effortless Priority Accounts Management with AdminDroid!
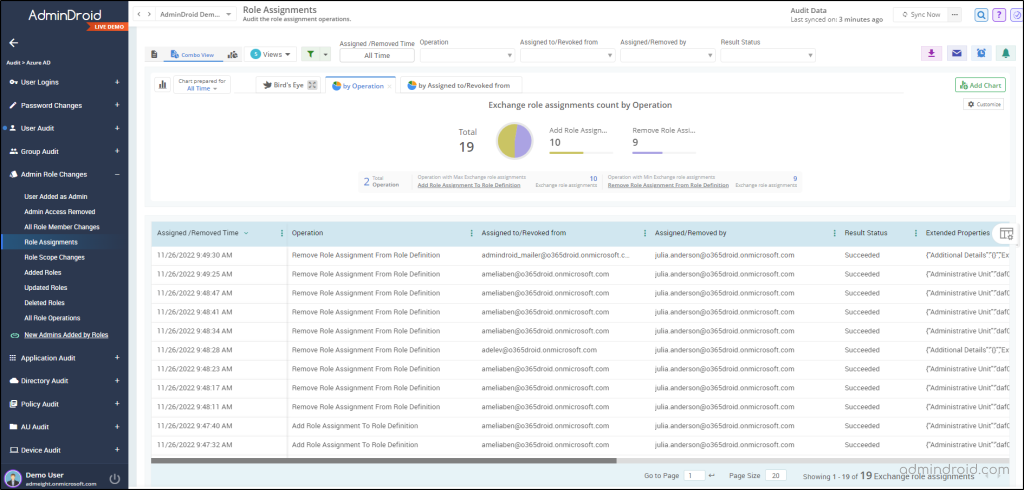
Monitoring critical accounts is essential for administrators who are unwavering in maintaining security measures. Amidst the multitude of monitoring options available, AdminDroid Microsoft 365 reporting tool harnesses its unmatched power to provide comprehensive insights into admin accounts through advanced features like scheduling, export, customizable reports, advanced filters and many more. AdminDroid offers dedicated reports on Microsoft 365 admin role changes, enabling users to track changes made to critical accounts there and then.
Stopping with that? No, AdminDroid has a lot more to offer you, making your Office 365 monitoring process hassle-free! AdminDroid Azure AD auditing reports make sure that no changes made to admin accounts are unnoticed. Additionally, AdminDroid’s dedicated report board offers detailed information on admin accounts such as,
- Admins mailbox information
- Monitor admins’ O365 license usage
- Admins login info
- Administrative role changes
- Admin settings
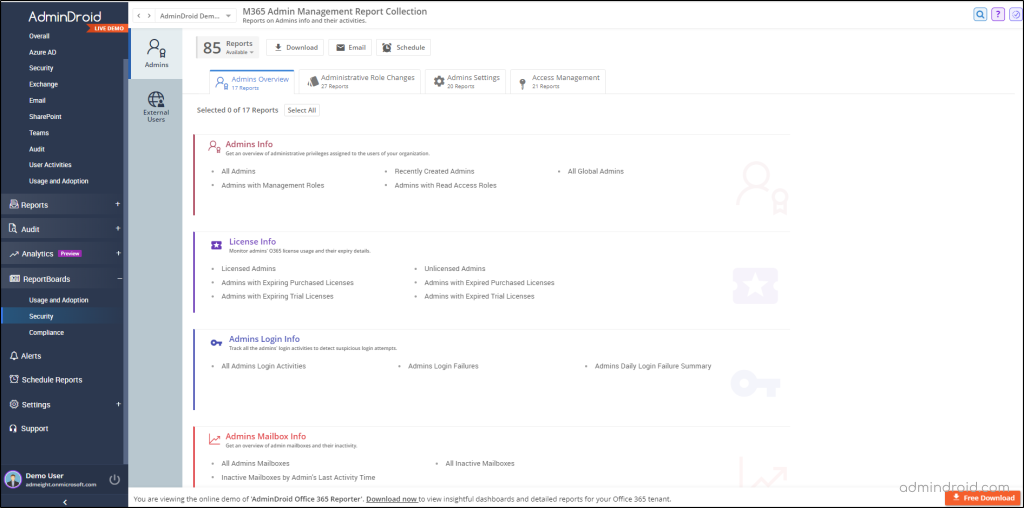
Also, AdminDroid comes with various admin reports such as admins with password expiry, recent password changed admins, admins with and without MFA etc. In addition, it is crucial to closely monitor domain configurations to ensure comprehensive security measures. However, there’s no need to worry as AdminDroid’s Azure AD management tool has you covered here!
Moreover, this powerful tool simplifies every administrative task significantly by offering a wide range of over 190 insightful reports. These reports enable administrators to effectively manage and monitor admin activities within their organization. Each report is thoughtfully designed, 🔎presenting data in visually appealing charts and graphs for easy analysis and decision-making. 📊
Get started with AdminDroid today and enjoy effortless Office 365 monitoring!






